
In the high-stakes world of international cyber-espionage, you’d expect digital masterminds to use unhackable encryption and complex security protocols. Instead, a massive North Korean IT operation, responsible for raking in millions of dollars, was recently dismantled because they protected their central hub with the most cliché password in history: “123456.”
The operation was blown wide open by an anonymous counterhacker who compromised a worker's device and shared the findings with the prominent blockchain sleuth ZachXBT. The resulting leak offers a rare, humanized look at the mundane "office life" of state-sponsored scammers.
The group didn't operate out of a dark basement with green code scrolling down screens. Instead, they ran their business like a high-pressure sales floor.
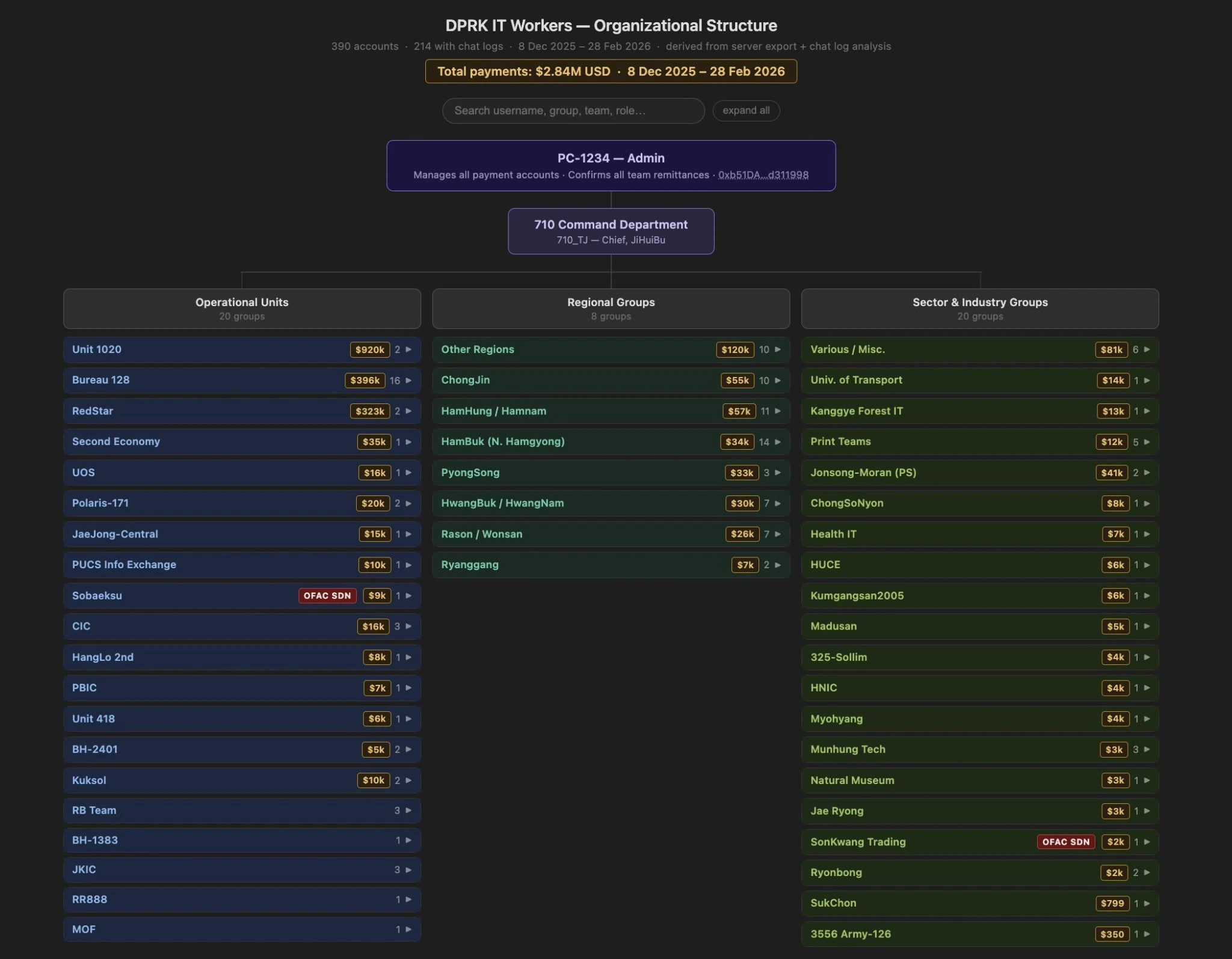
Using a site called luckyguys.site, a team of roughly 140 workers tracked their "wins." The leaked data included a leaderboard that ranked members based on how much crypto they had successfully brought in since December. In just a few months, the group had successfully accumulated $3.5 million, averaging about $1 million per month in revenue.
The workers weren't just hoarding Bitcoin for fun. The investigation traced the flow of funds from crypto wallets to Chinese bank accounts using everyday payment platforms like Payoneer. However, their lack of "operational security" was their undoing; these addresses were eventually linked back to known North Korean wallets that Tether had already blacklisted.
The leaked documents provided a glimpse into the specific personas these workers used to infiltrate Western companies.
One worker, using the alias “Jerry,” spent his days like many remote freelancers: browsing Indeed and firing off resumes. To hide his location, he used a VPN to access Gmail and applied for full-stack developer and software engineering roles.
In one particularly surreal discovery, an unsent email showed Jerry trying to land a gig as a WordPress specialist for a Texas-based T-shirt company. He was seeking $30 an hour for 15 to 20 hours of work per week, a modest request for someone part of a multi-million-dollar state operation.
Another member, known as “Rascal,” handled the more "creative" side of the business. His files contained:
While the "123456" password makes this group seem amateurish, the broader context is much more serious. North Korean state-backed groups have stolen over $7 billion in funds since 2009.
ZachXBT noted that this specific unit was actually less advanced than elite groups like AppleJeus or TraderTraitor, which carry out massive architectural hacks. However, this "low-level" group represents a different kind of threat: social engineering. By embedding themselves as trusted employees, they gain internal access that no firewall can block.
This exposure serves as a blunt reminder for the tech and crypto industries. When hiring remote talent, a polished resume and a friendly Zoom persona might just be a front for an operative half a world away, especially if they’re part of a 140-person team all sharing the same lazy password.